The digital age has accelerated a phenomenon where secrets, once protected, are now frequently thrust into the public domain. The term "leaked" itself carries a sense of secrecy. A leak can be deliberate, ranging from confidential documents to personal information. Understanding the nuances of "revealing" is crucial in navigating this complex landscape.
- Every leak, regardless of its motivation, has effects. Governments can suffer reputational damage as a result.
- Moreover, leaks often ignite public controversy around the topics they expose.
In a world where accountability is increasingly valued, the act of leaking secrets has become both challenging. It demands us to scrutinize our notions of privacy, power, and truth.
Compromised: Navigating the Risks of Information Leaks
In our increasingly interconnected world, the flow of information is a constant tide. But with this fusion, comes a new danger: unauthorized disclosure. Data breaches, hacks, and leaks are no longer just abstract concepts - they are a frequent reality. Every day, sensitive information about individuals, organizations, and governments is stolen. This has significant consequences, ranging from financial loss to identity theft, reputational damage, and even political instability. Understanding the nature of these leaks, their origins, and the impacts they have on individuals and society is crucial in our efforts to combat this growing challenge.
- Furthermore, it is essential to explore the policy frameworks that are in place to secure sensitive data and hold perpetrators accountable.
- In conclusion, we must strive for a digital environment that is both progressive and secure.
Unveiled
The term "leaked" gets thrown around a lot these days, often in connection with sensitive information or secrets. But what does it really mean? At its core, "leaking" implies the unauthorized release of something that was meant to be kept secure. This can happen through a variety of means, from hacking to negligent employees giving information. The context matters too: a leaked draft document is different from a top-secret government file.{
- Often, "leaked" is used more loosely to describe information that has come into the accessible domain, even if it wasn't deliberately released.
- Truly, the meaning of "leaked" depends on the specific situation and the intent behind the disclosure of information.
Leaked Data
A leak of a document or information can have severe implications for governments. The exposure of sensitive data can cause a variety of problems, including financial loss, reputational damage, and legal action. Individuals whose private information is compromised may become vulnerable to fraud. Organizations that experience a data breach may face regulatory fines, customer distrust, and operational disruption. The consequences of a leaked document or information can be long-lasting. It is therefore important to take steps to safeguard sensitive data and minimize the risk of a exposure.
When Something Gets Leaked: Understanding the Impact and Aftermath
In today's interconnected world, cyber leaks can have a devastating impact on individuals, organizations, and even governments. When sensitive information is compromised, it can trigger a cascade of harmful consequences. From reputational destruction to financial setbacks, the ripple effects of a leak can be felt far and wide. Understanding the potential impact of a leak is crucial for implementing effective mitigation strategies.
- Companies may face reputational ramifications, while individuals can experience identity theft. The public's trust in affected entities can be eroded, leading to a loss of investment.
- In the aftermath of a leak, it is essential to conduct a thorough assessment to determine the scope of the breach and identify vulnerabilities. Steps should be taken to contain the damage and prevent future occurrences. Transparency and ownership are crucial for restoring public confidence.
- Finally, understanding the impact and aftermath of leaks is essential for navigating the increasingly complex cyber sphere. By prioritizing security measures, promoting ethical practices, and fostering a culture of awareness, we can mitigate the risks associated with data breaches and protect ourselves in the digital age.
Unveiling the Truth: A Leak's Rise to Prominence
A leak can start as a mere whisper, shared in hushed moments. It might be confined to a small network of individuals, a piece of information transmitted from one person to another. But over time, this delicate nugget can evolve, gaining momentum as it travels. It hops from several channel to another, fueled by desire. Before long, what was once a secret hidden within walls can explode into the public domain, transforming from a mere speculation leaked synonym into a headline-grabbing scandal.
 Mara Wilson Then & Now!
Mara Wilson Then & Now! Devin Ratray Then & Now!
Devin Ratray Then & Now! Andrea Barber Then & Now!
Andrea Barber Then & Now!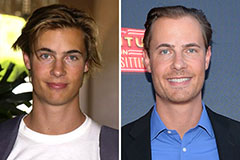 Erik von Detten Then & Now!
Erik von Detten Then & Now! Raquel Welch Then & Now!
Raquel Welch Then & Now!